
now doing business as Lumen
Network Security
In today's environment, security and risk management have become critical to the well-being of our nation. The CenturyLink Team has been—and will continue to be—an industry leader in working with your agency to meet this national priority. We have implemented a hierarchy of controls and management tools in the areas of personnel, systems and facility security, each of which are governed by a comprehensive set of security policies, standards and guidelines.
CenturyLink's extensive experience has shown that, in light of today's ever-changing climate of threats and vulnerabilities, a sound security position is best maintained by adopting a holistic view of risk management. This enterprise-wide approach to risk management, and more specifically, security practices, calls for:
- Centralized authority and policymaking
- Clear lines of communication
- Well-defined expectations
- Close collaboration among all parties
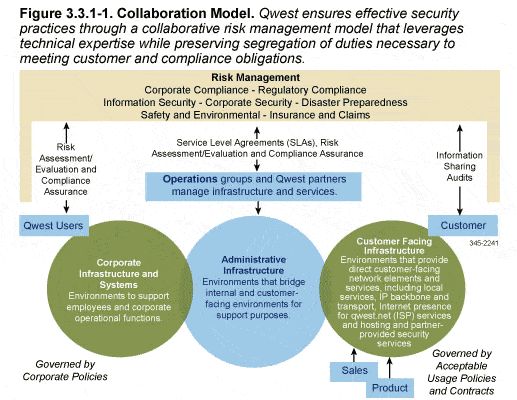
The illustration above displays an overview of our collaboration model, which provides the backbone for rapid identification of new threats and vulnerabilities. This approach allows us to create an action-oriented platform for reducing risks and managing security events.
As the cyber threat for federal customers has grown, so has the need for demonstrated security practices to comply with obligations such as the:
- Federal Information Security Management Act (FISMA)
- Department of Defense Information Technology Security Certification and Accreditation Process (DITSCAP)
To meet these demands, CenturyLink has evolved our security- and technology-related functions to ensure close organizational alignment and collaboration with more traditional industrial security programs.
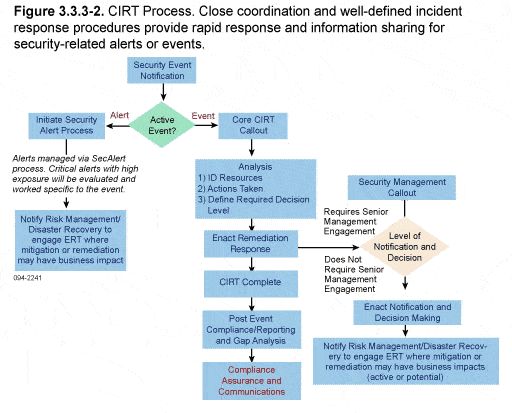
The illustration above provides an overview of how our well-defined, incident-response procedures allow for rapid response and information sharing. One of CenturyLink's key team members in this regard is SAIC.
SAIC demonstrated a history of proven capabilities in designing and delivering specific security services. Feedback from customers, our highly experienced staff and external auditors and consultants have shown that this team approach to security fosters a stronger recognition of risks, and allows for a more rapid response to threats.
